How to Easily Repair a Hacked Website – Complete Guide (2026 Update)
Is your website hacked? Most website administrators who contact us report symptoms such as their website redirecting or spam pop-ups on their website. This is naturally stressful. Let us set your mind at ease: you can repair your compromised website. Before we begin cleaning the website, we must first ensure that it has not been hacked. Scan your website with a security plugin to validate the attack. Once you’ve confirmed the hack, the next stages will be a lot easier. This article will walk you through the process of identifying and cleaning up malware on your website.
How do you know if a website has been hacked?
Before you can begin cleaning up your hacked website, you must first determine whether it has been hacked at all. Scanning is the most effective approach to confirm a hack, but you should also be aware of the indicators of a hack to assist you in identifying a hack.
Signs of a hacked website
It is not always possible to tell if a website has been hacked. The symptoms of a hack can vary depending on the type of malware, or they may not emerge at all. Malware might also creep up on you if you don’t know what to search for. Given that hacks deteriorate over time, it is critical to detect them as soon as possible. As a result, you should be aware of the indications to check for if your website has been hacked. The following are some of the most prevalent symptoms of hacked websites.
Examine your Google search results.
Google is really effective at detecting malware. Because they want to promote a safer browsing experience for their search engine users, their bots are constantly on the lookout for viruses when they crawl your website. If your website is hacked, it is likely that it will appear on Google quickly. Google your website particularly to check your Google search results. For example, if you want to search Twitter on Google, enter site:twitter.com. You can also use this after your search query to find specific terms on your website. In the event of a hack, you will notice the following anomalies in your Google search results.
Meta descriptions that are unsuitable
Meta descriptions are the brief summaries that appear beneath search results and clarify what the web page is about. Typically, it will be anything you specify or a relevant excerpt from your website. However, if your website has been hacked, your meta description may contain invalid numbers, Japanese characters, or even irrelevant keywords.
Indexed pages
Hacks frequently result in the addition of spam pages to your website. You can see if this has happened by looking for your website on Google and seeing if the number of indexed pages matches the number of pages on your website. If the number is much higher, this indicates that spam pages are being indexed on your website, which is a symptom of a hack.
Google’s Exclusion List
As previously said, Google is dedicated to providing a safe experience for its users. As part of this, they established the Google Safe Browsing project, which searches websites daily and warns them if malware is detected. The Google blacklist can appear as a warning in the search results or as a large red screen before you access the page. Some of the cautions are as follows:
- Phishing site ahead
- This site contains malware
- This site has been reported as unsafe
- This site may be hacked
- Deceptive site ahead
If you observe any of these indicators in your website search results, your website has most certainly been hacked.
Check your website for issues
Some website hacks produce no symptoms at all. However, some symptoms may manifest on your website. The visible areas of your website that you visit on a daily basis can tell you a lot about its general health. So keep an eye out for some of these signs on your website.
Pop-ups with spam
If you notice an uninvited pop-up on your website, it is most certainly malware. These spam pop-ups are designed to either direct your clients to spam sites or to trick them into downloading malware disguised as freebies. While spam pop-ups are a significant indicator of infection, they can also appear as a result of your website’s ad networks being enabled. If you see this, scan and sanitise your website as soon as possible.
Redirections to spam websites
Malicious redirection is a major issue. They can get disorganised because the login page, like the other pages on the website, sometimes redirects to other websites. If this happens, you won’t be able to log in or stay on your website long enough to figure out what’s wrong. Automatic redirects to spam sites are a dead giveaway that your website is infected with malware.
Phishing websites
Phishing is a type of social engineering assault in which users’ personal and financial information is obtained through spoofing techniques. Typically, a phishing page attempts to look like an official page and includes a bank logo or branding to appear more credible. If you notice phishing pages on your website, it is almost certainly the result of a website attack.
Broken pages
If you encounter pages with weird code at the top or bottom, or if the elements on the page appear disorganised, this could be a symptom of infection. While broken sites can arise as a result of a faulty plugin or theme, malware is a real danger.
Death’s white screen
When you visit your website, your browser becomes blank, resulting in the white screen of death. It’s a frustrating scenario because you don’t know what went wrong or how to remedy it. When this happens, there is no way to enter your wp-admin, and you are locked out of your own website.
Investigate the backend of your site.
Your website’s backend might also tell if it has been hacked. You can also look for symptoms on the backside. However, if you are not an expert or understand code logic, these can be difficult to spot.
Activity log
Examining your website’s activity log is a useful technique to look for symptoms on the backend. You can use a plugin like WP Activity Log to monitor the activity on your website and see if there is any unusual activity.
Unusual code on your website
Your website is made up of code, and malware can be hidden within the code. As a result, it may appear harmless anywhere on your page. If you observe any modifications to the website code or unusual code on your website, you must act quickly to confirm the hack before it worsens.
Unusual user behaviour
If a person exhibits strange behaviour, such as making too many new posts in a short period of time or changing the settings, this could be a sign of a hack or a compromised account, which can lead to a hack.
Escalation of privileges
Hackers frequently leverage current website users to gain access to their accounts and escalate their privileges in order to gain access to your entire website. This is why you should be on the lookout for any website users whose privileges have been unexpectedly escalated.
Fake plugins
The malware’s creators do not want you to discover it. As a result, they conceal it under legitimate-looking directories such as themes and plugins. Malware spreads using fake plugins. Fake plugin directories contain only one or two files and are oddly labelled.
Keep an eye out for any contact from your web host.
Your web host is concerned about the security of your website since a hacked website on their servers might bring them a lot of problems. As a result, the majority of web hosts analyse their websites on a regular basis. If your web host sends you an email stating that malware has been identified, or if they suspend your site citing malware as the reason, it is a pretty good bet that your website has been hacked. Another thing to keep an eye out for is server use. If your web provider informs you that your server utilisation has increased despite no major change in your website traffic, this could be due to malware.
Take note of visitor feedback.
Hackers will sometimes conceal spyware from website administrators. So, while you may not notice any of the symptoms listed, your visitors may. If any of your visitors complain about spam pages on your site or the site functioning strangely, take this input seriously and run a scan as soon as possible. Visitors frequently notice symptoms that the administrator overlooks, such as receiving spam emails from your website or being diverted when browsing your site. Even if the feedback is a complaint about your website not loading quickly enough, you should investigate it because even minor symptoms might be a sign of infection.
Examine your website’s metrics.
Your website analytics may inform you more than just about customer behaviour and conversion rates. Malware indications might be found in your website analytics if you know what to look for. Here are a few things to keep an eye out for.
Search Console
The Google Search Console searches your website on an irregular basis and can detect malware. If it detects malware, it will flag it, and the details will be displayed under the ‘Security problems’ tab.
Increased traffic from specific regions
If you notice an unexpected increase in traffic from specific regions or nations that are not necessarily part of your target geography, this could be a symptom of unwanted traffic on your websites, such as bots or hackers. Traffic spikes can be a precursor to malware or a sign of traffic flowing to spam pages. As a general guideline, it is best to check these on a frequent basis.
Pay close attention to issues of performance.
When your website is hacked, you may not necessarily see a large red warning indicating it has been compromised. It can also manifest as subtler, less obvious symptoms. These symptoms might be of any kind, but performance concerns with your website are simple to overlook if you aren’t on the lookout. Pay close attention to the following concerns, since their presence may indicate the presence of malware on your website.
The website is slow.
When your website is hacked, malicious code and files are put into it. While harmful code can wreak havoc on your website, its mere presence can cause problems. Your website servers may become overburdened as a result of the malware’s additional data, and the loading time of your website may be impaired. Certain hacks, such as bot assaults, might flood your website with requests, increasing the download time even further.
The website is inaccessible.
Malware might render your website inaccessible to both users and visitors. DoS attacks or redirect hacks might render your website or sections of it inaccessible. Although it is impossible to ignore the fact that your site is inaccessible, it is critical that you acquire access as soon as possible so that you can clean it up.
Emails from the website are routed to the spam folder.
Because email providers strive to provide their users with a safe experience, they filter incoming emails and mark them as spam if they detect anything suspect about them. Websites that have been hacked jeopardise their users’ internet security. As a result, any emails received from hijacked websites are routed immediately to the spam folder. While there are other causes for messages winding up in the spam folder, such as spam keywords or overtly promotional content, malware is a major one. If emails sent from your website are frequently ending up in spam folders, it is possible that your website has been hacked.
Examine your hacked website.
Simply suspecting a hack is insufficient; you must confirm the hack before proceeding to clean it up. Scanning is the most effective method for diagnosing your website and confirming a hack. You can scan your website in a variety of ways.
Use an internet scanner to scan your website.
Online scanners, such as Sucuri Site Check, look for viruses in the visible areas of your website. While not totally effective, it might be an excellent starting point in your diagnostics approach. Certain types of malware, such as the pharma hack or the Japanese keyword hack, can appear on your website’s visible code since these hacks affect the frontend code. However, keep in mind that online scanners cannot be your primary tool for troubleshooting your website. If you get a positive result for malware, you can be confident your site has been compromised. A clean chit, on the other hand, does not imply that your site has not been hacked.
Manually scan your website
You may manually scan your website for viruses. However, we strongly advise against taking this course of action. We’ve included this part to make sure you’re aware of all your options, but it’s not a good idea unless you know exactly what you’re doing. There’s a chance you’ll overlook anything or mistake legitimate code for malware. Furthermore, there is no malware blueprint. Junk code can be anything and can be found anywhere on your website.
So, in order to detect malware, you must first be familiar with the code. Having stated that, the first step in manually detecting malware is to search for recently updated files on your website. You can accomplish this using the File Manager. If you haven’t made any changes to the file that appears, it’s probably malware. As previously stated, the best course of action is to employ a security plugin such as MalCare. MalCare is thorough and speedy, which is crucial because hacks must be addressed swiftly. Once you’ve determined whether or not your site has been hacked, all you need to do is upgrade to clean it up.
To execute, some simple diagnostics
While scanning is the most effective technique to confirm a hack, there are also other simple ways to diagnose a hack on your website. These diagnostics are not as precise as security scanners, but they can provide useful information about the health of your website.
- Visit your website in an incognito window and see if any symptoms appear.
- When you do a Google site search, look at the amount of pages on your website. If the number is significantly higher than the actual number of pages, it could indicate that your site is being indexed with spam pages.
- Examine the activity log for any instances of unexpected user privilege escalation or ghost users.
- Examine the wp-content folder for any fraudulent plugins. Fake plugins typically have unusual names and simply one or two files.
- Check to see if any of the plugins or themes you use have any reported vulnerabilities. If so, please update these as soon as possible.
These tests can detect symptoms and provide you with a good sense of your website’s security. However, you should employ a security scanner to check the attack and to be thorough.
How do you fix a hacked website?
You should have received confirmation of the hack at this point. This information will aid you in the following stage, which is cleansing your hacked website. There are several ways to repair your hacked website, and we’ve highlighted the three most prevalent ones.
Employ a security professional.
Hiring a security specialist to physically clean your compromised website is another option for repairing it. While this is not the ideal option, it is still preferable than a do-it-yourself clean-up. Expert cleaning services take time because they are done by hand. As a result, they are pricey. While we cannot guarantee the quality of services supplied by any security solution,
Manually restore your hijacked website.
Manual cleanups are inefficient and time-consuming because, unless you are a security specialist, much of what you do will be trial and error. This takes time, which may aggravate the hack. However, if you make an unintentional error, it can exacerbate your predicament. We frequently receive anxious calls from website administrators who have attempted to clean up their website manually and accidentally broken it. This takes far more time to repair than using any other method in the first place. If you still need to manually repair your hacked website for any reason, here’s how.
Check that you have access to your website.
If your web provider has suspended your account and you no longer have access to your website, the first thing you should do is regain access. You can email your web host and ask for access for cleanup purposes. If they do not comply, you must utilise FTP to obtain a duplicate of your website so that you can clean it locally. You can also request a list of malware on your website from your web server. You can read our tutorial to learn more about how to deal with a web host account suspension.
Make a copy of your website.
The next step is to create a backup of your website. Even if it has been hacked, you still have a website. You can always restore it if something goes wrong during the cleanup. However, without a backup, you risk losing all of your website data if things don’t go as planned.
Download the repository’s WordPress core, plugins, and theme files.
You’ll need a reference before you can begin cleaning. You’ll need to download clean instals of the WordPress core, plugin, and theme files for this. They are available for download from the WordPress repository. However, be certain that you download the same versions as those on your website. Otherwise, there may be differences in the code, making it impossible to compare files.
Reinstall the WordPress core software.
Now comes the difficult part. You must reinstall the core files on your website. Begin by navigating to the wp-admin and wp-includes folders. Because these two folders do not contain any user content, you can simply replace them. After that, look in the wp-uploads folder. There should be no harmful PHP files in this folder. So, if you find any, delete them. You must now begin looking for unusual code in the files. Examine the following files in particular:
- index.php
- wp-config.php
- wp-settings.php
- wp-load.php
- .htaccess
We understand that unusual code is a broad description, but there is no single type of code that indicates malware. As a result, you must exercise extreme caution. Do not delete anything until you are completely certain it is malware, especially since they are vital files.
Plugins and themes that are clean
After that, it’s time to tidy up the plugin and theme files. These files can be found in the wp-content folder. You must contrast the clean installs with the files on your website. This can take some time, so we recommend using an online diffchecker for this. This will assist you in identifying any discrepancies between the two files. Begin by looking for the active theme files listed below:
- header.php
- footer.php
- functions.php
Because themes and plugins can be customised, the changes may appear to be extra code. As a result, deleting any code that differs from the clean instals may result in the loss of customizations or the inability to use plugins and themes.
Clean up the database tables.
The database is the final step in the core clean-up procedure. To clear out the database tables, you’ll need phpMyAdmin, which allows you to download and access the database tables as well as inspect the code. Examine the database tables to check if there is any strange code or scripts. Begin with your existing pages and posts because you already know how they should look. They can be found in the wp-posts table. Look for newly generated pages and posts, and see if there are any that were not created by you. You can then look at the wp-options table. These two tables are frequently infected with malware.
Take out all of the backdoors.
Cleaning up the data is only half of the battle. The malware entered your website through backdoors, and your site is still vulnerable as long as the backdoors remain. The next step is to eliminate all backdoors. Backdoors can be found everywhere on your website, therefore you must extensively search for them. Popular backdoor keywords include eval, base64 decode, gzinflate, preg replace, and str rot13. Note: These keywords are frequently found in backdoors, but they also have certain genuine usage in plugins and themes, and removing them may cause difficulties with the extensions’ functionality.
Upload new, clean files.
It’s time to re-upload all of your cleaned files to your website. You must first delete the existing files and database before re-uploading all of the files that have been cleansed. You can do this with File Manager and phpMyAdmin. Given that this method is identical to restoring a manual backup, you can refer to our detailed tutorial on how to do so.
Delete the cache
The final step is to clean the cache on your WordPress website. Cache is used to make duplicates of your website in order for it to load faster. However, if your website has been compromised, the cached versions are likely to include malware as well. As a result, even after the cleanup, your website may still contain malware. To completely eliminate spyware from your website, erase the cache completely.
To confirm, use a security scanner.
The worst is over, and the cleanup is complete! All that remains is to employ a security scanner to ensure that your website is malware-free. This stage is critical since it determines whether or not your attempt was successful. If yes, you may proceed. However, if this is not the case, you will need to recheck everything. It is best to invest in a security solution in this instance.
Hacked Website Repair: Symptoms of a Hacked Website
- On your website, suspicious and unknown links, files, admin users, web pages, tables, and scripts emerge.
- Pop-ups and advertising that lure customers to dubious domains contaminate your website.
- The website becomes unresponsive and slow.
- Even if the number of connections is small, the server is under a lot of strain.
- Users have complained about their credit card information being stolen from your website.
- As a result of the Japanese Keyword Hack or the Pharma Hack, gibberish text shows on your site.
- Your account may be banned or disabled if you use third-party hosting.
- Users are advised not to visit your website by search engines.
- Your website’s passwords have been changed, and logs suggest that brute force logging attempts have occurred.
- Your server has unidentified plugins and extensions installed.
- Several spam emails were sent from your website’s mail server.
- On internet forums, the data from the website is for sale.
- Data is being sent to strange sites, according to traffic logs from Wireshark or other packet capture tools.
Hacked Website Repair: Malware Removal
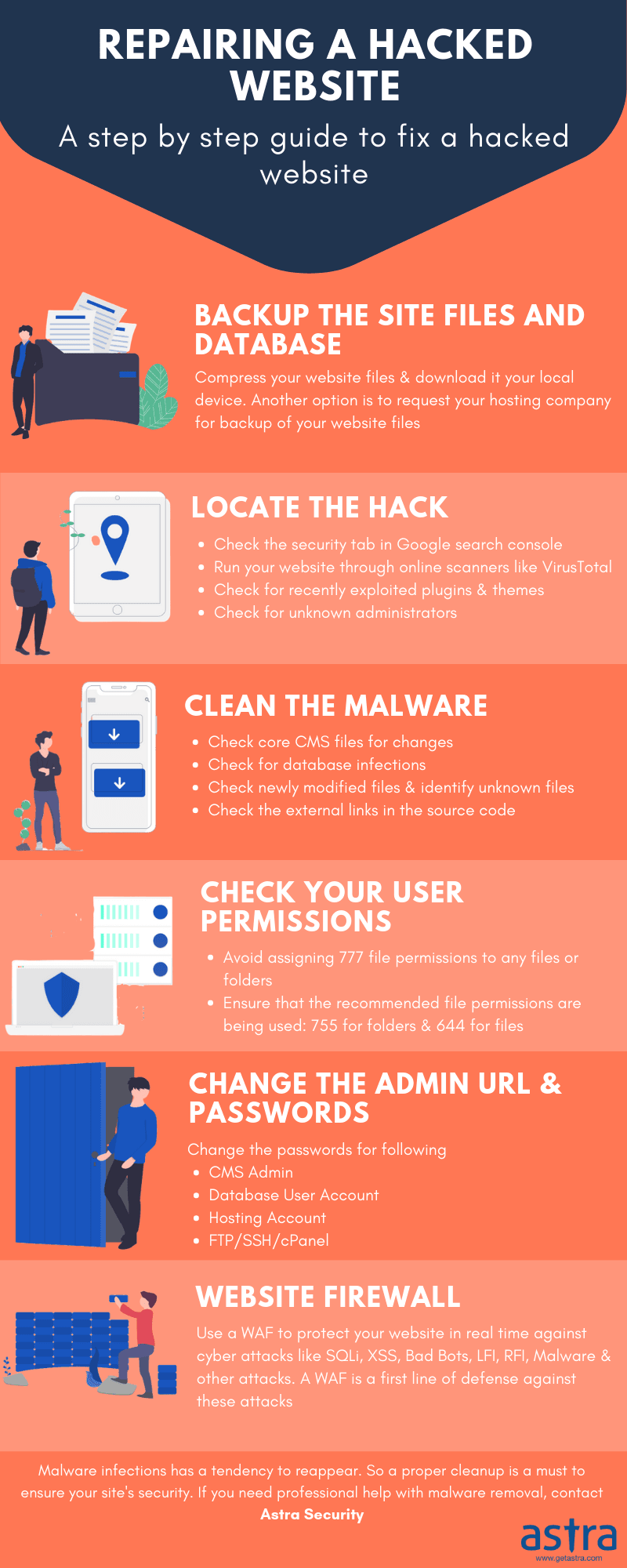
- Step 1: Create a full backup of your website. After that, put your site in maintenance mode.
- Step 2: Look for the cause of the infection. A script, file, or web page could be involved. To determine base64 encodings, examine the source code. Keep an eye out for any new plugins or extensions.
- Step 3: If the website has been blacklisted by search engines, use Google Console to determine the source of the infection. Also, make sure to remove any unrecognized admins. If you’re still having trouble, try using online malware scanners like Astra.
- Step 4: Remove malicious code lines from compromised files. Remove all suspect tables from the database. If it’s a sensitive file and you’re not sure what the code does, simply comment it out and ask for assistance.
- Step 5: Once your site has been cleaned up, don’t forget to submit it to Google for blacklist removal. Furthermore, the source of the hack must be identified and fixed so that the infection does not repeat. For more information, please see the info graph below.
While these are general hacked website repair processes, certain CMS-specific hacked website repair instructions are provided below.
PHP Malware Removal
Examine the database first for PHP hacked website repair. First, create a backup of the database. Look for any strange tables like ‘Sqlmap’ using a programme like phpMyAdmin. Additionally, scan the contents of the tables for any suspicious links, malicious code, and so on. If an entry is detected, remove it or, if required, the entire table. After that, check to see if the site is still operational.
If that’s the case, you’ve successfully deleted the malware from the database. Use the following command to locate base64 encoded malicious code in PHP files to detect infection: discover -filename “*.php” -exec grep “base64′′”; -print output.txt Other obfuscation techniques, such as FOPO, are sometimes employed in addition to base64 encoding. I removed any unidentified PHP scripts. If you’re not sure what the code performs, comment it out and seek malware eradication assistance.
It is critical for PHP to block harmful functions that can aid attackers in Remote Code Execution. This can be accomplished with a single command: “show source, system, shell exec, passthru, exec, popen, proc open, allow url fopen, eval” Sometimes error messages reveal important information that attackers can use to breach your site.
To disable such errors, include the following code into the php.ini file: log errors=On display errors=Off error log=/var/log/httpd/php error.log This code blocks the display of problems and instead logs them to a php error.log file, which you may use for debugging. Last but not least, ensure that all input received by your server via PHP forms, values, and so on is filtered. Unsanitized input might devastate your website.
WordPress Malware Removal
In order to fix a WordPress hacked website, review the core files first because infection removal from these files is simple. In addition, review the system logs for any changes made to the files. This can aid in the detection of a malware infection.
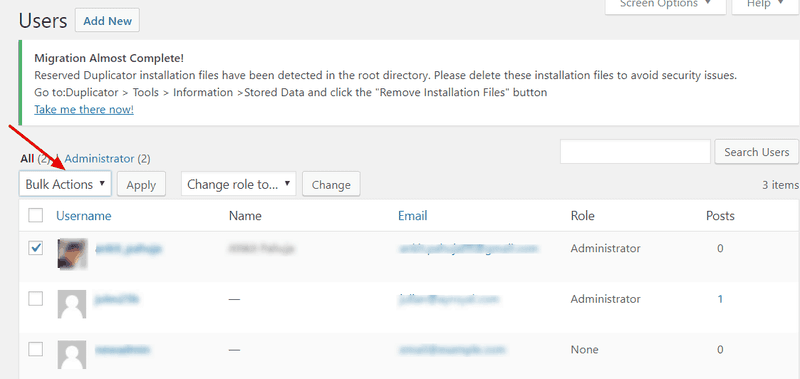
If the core file is infected, simply replace it with a new one from the official repository. The same is true for theme files. Avoid editing important files and folders like wp-content and wp-config. If the malware has created new WordPress user accounts, they should be deleted as soon as possible. Look for any new or suspicious user accounts and delete them. To get rid of unknown users:
- Open the wp-admin dashboard and navigate to Users>All Users.
- From the checkbox select the user you wish to remove and expand the “Bulk Actions” dropdown.
- Finally, select the “Delete” option and then “Apply” the settings.
Also, look at the picture files, as malware such as the bak.bak/Favicon malware regularly targets WordPress sites. Examine the wp-uploads folder and individually scan each image. To do so, move the.ico files to a folder and rename them.txt. Now, open these text files. If the content appears to be gibberish, as shown in the image, the files are clean; otherwise, if the text file contains PHP code, proceed with the above-mentioned steps for WordPress hacked website repair. Last but not least, don’t forget to disable XML-RPC in WordPress.
![]()
Before applying any manual fixes or updating plugins, clone your site to a staging environment. This lets you test changes safely without risking downtime on your live site. Many hosts (Kinsta, WP Engine, SiteGround) offer one‑click staging. Always clean and test there first.
Advanced Security Strategies for 2026: Beyond Basic Cleanup
As cyber threats evolve, so must your defense. Here are five advanced tactics to harden your site against future attacks:
- Implement Web Application Firewall (WAF): A WAF like Sucuri or Cloudflare blocks malicious traffic before it reaches your server. It stops SQL injection, XSS, and bot attacks at the edge.
- Use a Password Manager with 2FA: Enforce strong passwords for all users and enable two‑factor authentication. Plugins like Wordfence or Google Authenticator add this layer easily.
- Limit Login Attempts: Brute force attacks are common. Use plugins like Limit Login Attempts Reloaded to block IPs after repeated failures.
- Disable File Editing in wp-config.php: Add
define('DISALLOW_FILE_EDIT', true);to prevent attackers from editing theme/plugin files directly if they compromise an admin account. - Regular Offsite Backups: Store backups in a separate location (e.g., Amazon S3, Google Drive) using plugins like UpdraftPlus. Daily backups ensure you can restore quickly even if malware strikes.
Attackers now use generative AI to create convincing fake login pages and emails. Always verify URLs, use security headers, and train your team to recognize subtle typosquatting attempts.
Real‑World Case Study: How a Small Business Recovered from a Major Hack
Background: A boutique e‑commerce store running WooCommerce was hacked via an outdated plugin. Attackers injected a backdoor and sent spam emails, causing the host to suspend the account. Traffic dropped 92% in one week.
Recovery Steps: The owner used MalCare to scan and clean the site. They restored a clean backup from 3 days prior, then manually removed suspicious files. They changed all passwords, installed a WAF, and set up daily backups.
Result: Within 48 hours, the site was back online. Google blacklist was removed after 5 days. Six months later, the site had stronger traffic than before, and no further incidents occurred. The key lesson: quick action and layered security pay off.
Quick Reference: Hacked Website Recovery Checklist
- ✅ Confirm hack via security scanner (Sucuri, MalCare, Google Search Console)
- ✅ Create full backup (files + database) before any changes
- ✅ Put site in maintenance mode to hide from visitors
- ✅ Identify and remove malicious code (use diff tools for core files)
- ✅ Replace core WordPress files with fresh copies
- ✅ Reinstall themes/plugins from trusted sources (delete unused ones)
- ✅ Scan database tables for suspicious entries (wp-posts, wp-options)
- ✅ Delete unknown admin users and reset passwords
- ✅ Remove backdoors (search for eval, base64, gzinflate)
- ✅ Clear all caches (browser, server, CDN)
- ✅ Re‑scan to ensure malware is gone
- ✅ Request Google review via Search Console
- ✅ Harden security (WAF, 2FA, limit login attempts)
- ✅ Set up automatic offsite backups
What is the impact of a hacked website?
A hack can result in the blacklisting of your website, the suspension of your web host account, and the loss of your website. But is that it? The long-term ramifications of a hacked website far outweigh the immediate consequences. If not addressed promptly, the consequences of a hack may get exponentially worse. Here are some of the ways a hack could harm you:
- Revenue decline
- Traffic decline
- SEO rankings are falling.
- Customer dissatisfaction
- Brand reputation damage
- Costs of cleanup
- PR costs
- Legal issues
This is far from an exhaustive list. A hacked website can have far-reaching consequences, depending on your website, the nature of your business, and the data on your website.
How to revert the damage of a website hack?
A website hack has a wide-ranging impact on your organization and users. As previously noted, once a website is hacked, there is already a significant amount of damage. You’ll need to take action to undo the damage. Here are a few things you may do to recover from a hacked website.
- Examine your website for flaws.
- Request that Google removes your website off the blacklist.
- Change all of your passwords and use strong passwords.
- Examine all user accounts for any privilege escalation.
- Never use unlicensed themes or plugins.
- Use a security plugin in conjunction with a powerful firewall.
How to prevent your website from getting hacked again
Malware is no longer present on your website. But did you know that a website that has been hacked is more likely to be hacked again? You could spend hours or days cleaning up your website only to discover another hack in a few of weeks. This can be disheartening, but there are precautions you can take to avoid future hacks.
Update your website
Everything on your website should always be current. It is critical to ensure that all of your themes, plugins, and the WordPress core are updated to the same version as soon as possible. The reason for this is straightforward: updates address critical software problems. If you ever examine the changelog for a recent upgrade, you’ll see a list of issues and faults that were addressed in the new version. These weaknesses are typically discovered by security researchers, who then notify the theme’s or plugin’s designers, allowing them to address them immediately.
After installing the patch, hackers can attack any website that employs the flaw-prone code. Unfortunately, many websites are not updated frequently enough due to their owners’ fear of breaking something. This is true, yet the expense of not keeping your website current outweighs the time required to maintain it current. Additionally, there are secure methods for updating your website. You can create numerous backups of your website in order to recover it if you make an update error.
However, the most secure method of making modifications to your website is through the usage of a staging server. Before deploying new features and updates to your website, you can test them on a staging server. This way, you can make modifications without jeopardising the website’s integrity.
Make your WordPress site more secure.
WordPress gives website owners a list of things they should do to keep their sites safe. This is called “WordPress hardening,” and it includes things like using strong passwords and two-factor authentication to make sure your site doesn’t get taken over. Take a look at how to harden your WordPress site to get more detailed instructions on how to do the same thing.
Use two-step authentication.
To add an extra line of defence to your login page, you can use two-factor authentication. This means that brute force attacks on your login page are less likely to happen. In most cases, after you enter your username and password, two-factor authentication will ask you for a one-time password so that your website is even more safe from hackers.
It’s time to put in SSL.
SSL is a type of encryption that protects any communication between your website and other people. When you put an SSL certificate on your website, you make sure that hackers can’t get their hands on any of the data that you send or receive from other servers. The use of SSL also helps you improve your SEO efforts because Google is now actively penalising sites that don’t use SSL.
Use strong passwords
Make sure your passwords are strong. Even though this may seem like common sense, weak passwords are still one of the most common reasons for websites to be hacked today. Admins usually pick a simple password so that they can remember it, but it’s not always the case. But doing so could make your website less secure. We suggest that you use a password manager so that you don’t have to remember a strong password every time you want to log in.
Reset user accounts
Hacks are often caused by user accounts. You have one account that hackers can get into. They can then get to the rest of your site through the account. Change the passwords for each account once in a while to make sure that they are safe.
How was your website hacked?
Because your website is entirely composed of code, hacks are common. Because no code can be guaranteed to be error-free, and no website can be guaranteed to be 100 percent safe. However, this does not mean that hacks cannot be prevented in the first place. Indeed, with the appropriate safeguards in place, you can effectively secure your website. Therefore, if you’re wondering how your website was hacked, the most likely reason is one of the following.
Undetected backdoors
Backdoors, as discussed previously, offer a substantial risk. Backdoors are essentially weaknesses in the coding of a website that hackers exploit to obtain access. Typically, these backdoors are installed using malware. Due to the fact that criminals design malware with the intent of remaining undetected, backdoors typically go undetected unless you utilise a comprehensive security plugin.
Themes and plugins have issues.
Your theme and plugin files may have security flaws that can be exploited to take control of your website. Vulnerabilities are coding mistakes or oversights in websites caused by human error. Vulnerabilities are an inherent part of life. Hacking, on the other hand, can be avoided by continuously updating your website. While developers work swiftly to patch vulnerabilities as they are discovered, you must update your themes and plugins to obtain the patch. If you’ve installed a robust security plugin, such as MalCare, it will automatically discover vulnerabilities and assist you in updating themes and plugins directly from the dashboard.
Poor user management
If every user has more access than they require, or if their accounts are not secure, this can result in a hack. The prudent course of action is to adhere to the least privilege principle and to allow access only when it is absolutely necessary. Additionally, it is vital to remove expired or inactive user accounts, as hackers can use them to get access.
Web host issues
While this is a rare occurrence, your web server may be responsible for a website hack. This attack could have originated in cPanel or one of the software packages utilised by your web server. When this happens, all websites hosted on the web host’s servers become hacker-friendly. If you are unable to find any reason for your website being hacked, check for recent correspondence from your web provider. The majority of web hosts tell their customers if they encounter any issues on their end.
Unprotected communication
If your communication is not encrypted, it can be intercepted by hackers or anybody else on the same network as you. To avoid this, it is vital to use SSL on your website. SSL encrypts connection between your website and its visitors, guaranteeing that no sensitive data or information is intercepted.
Why do websites get hacked?
Websites are hacked for a variety of reasons by attackers and criminal actors. However, the underlying motive for website hacking is the recognition of the value of every website. When a website is hacked, it includes resources that might be used for malicious purposes. Small websites can be used as botnet nodes or their data might be used in phishing scams. Due to the ease with which bots can be operated, brute force attacks require little effort.
Hackers require extremely little effort to gain access to your website, yet the reward is still fairly significant. Certain hackers may breach into websites in pursuit of personally identifiable information or financial data that can be exploited. Given that hackers nearly always have nothing to gain by attacking your websites, the onus of security rests solely on the website administrator. To safeguard your website against potential assaults, it is recommended that you utilise a security plugin.
Hacked Website Repair: Preventive Measures
- Admin folder should be renamed to some random user name. If your admin folder’s URL was previously www.abc.com/admin/, rename it to www.abc.com/random123/. The following instruction will show you how to do it.
- Hackers can view sensitive files and use them to hack your site if directory indexing is enabled. As a result, stop directory indexing by adding the following code to each directory’s.htaccess file: -Indexes -Options
- Make sure your CMS is up to date, regardless of whatever one you’re using. It’s a good idea to keep it updated from the official site to avoid website hacking.
- Attackers can’t get to your important files if you don’t use proper file permissions. Set the file permissions to 644 or 444 at all times. Set the permissions to 444 for important files like config.php, index.php, admin/config.php, admin/index.php, and system/startup.php.
- Make sure the site doesn’t have any hardcoded or default passwords. Use only well-known themes, extensions, and plugins.
- Always choose a secure hosting package over a low-cost one. The plan may appear inexpensive at first glance, but it could end up costing you a lot of money in the long run if your website is hacked. Also, make that the server is configured correctly and that there are no open ports or server misconfigurations.
- SSL not only secures communication between users and your website, but it also aids in SEO. For your website, obtain an SSL certificate and install it on your server. After that, make sure the website constantly redirects to https rather than HTTP. To do so, edit the.htaccess file with the following code:
# Redirect HTTP to HTTPS RewriteEngine On RewriteCond %{HTTPS} off RewriteCond %{HTTP:X-Forwarded-Proto} !https RewriteRule ^(.*)$ https://%{HTTP_HOST}%{REQUEST_URI} [L,R=301]
Repairing Hacked Website: Step-By-Step Guide
There are two ways a compromised website can be repaired-manually or via a plugin.
Manually Repairing a Hacked Website
We don’t suggest this corrupted form of website repair and we’ll discuss why.
- This technique necessitates a significant quantity of technological know-how. You must be familiar with the backend of a WordPress website. There aren’t very many! WordPress was created to make it simple for anyone to create a website without requiring any coding knowledge. If you don’t know enough about WordPress’s inner workings, you should avoid doing this.
- Diving into the site’s archives and directories to make modifications is quite risky. Your site will crash if there is a tiny coding error or omission.
- This method is time-consuming and takes concentrated work to manually scan the website, locate, and remove the virus. Because it’s difficult to detect each current instance of malware, hackers upload their infection into multiple files and servers in various conditions.
- Finally, look for code that has been identified as dangerous, such as ‘foundation 64’ and ‘eval.’ If a programmer creates new code or hides it well, you won’t be able to find it. If you identify the corrupted files, you must uninstall or delete the malicious code that was introduced. Because some files are interdependent with other files, uninstalling them will cause your site to crash. As a result, this method is ineffective the majority of the time.
- Rather of going through this process, we recommend adopting a dependable and effective WordPress Protection Plugin that will scan the site and remove any viruses. On the market, there are various plugins that provide malware removal services for testing and WordPress. However, not all of them are effective and have sufficient defence. To restore the website’s functionality and provide effective protection, we’ll use the MalCare WordPress Security Plugin. We’ll describe why we chose MalCare and how we’ll use it in the future.
How To Prevent Hacks on Your WordPress Site
To protect your website against hackers, we’ll give you five easy steps:
Use a Security Plugin
Always have a security plugin active on your WordPress account. Hackers tend to prey on easy targets, regardless of how large or small the site is. There’s a good chance they’ll try a few times and then move on to the next target once they notice you have basic website security measures in place. MalCare is a programme that we recommend you download.
It will scan your website for malware on a regular basis and notify you if it detects anything suspicious. It will install a firewall that protects the website and prevents hackers from accessing it. It also automatically adds password security to your site, decreasing the number of times a visitor has to enter the correct credentials. This prevents brute-force attacks, in which hackers attempt to guess your login credentials in order to get access to your website.
Update Your WordPress Site Regularly
WordPress is a reliable platform for creating websites. However, we must keep in mind that each WordPress platform makes use of themes and plugins created by third-party developers. Any program’s security issues will worsen over time. As a result, the vulnerability bug is patched by developers, and a patch with an enhanced version is released. On your WordPress dashboard, you’ll notice an upgrade option.
After you deploy the upgrade, the security flaw or vulnerability will be addressed. However, if you choose not to upgrade, you leave your site vulnerable to attacks. This is how the developers officially reveal what the issue was and how it was fixed before releasing an upgrade. As a result, hackers are aware of this flaw and are on the lookout for it. They find websites and launch assaults using outdated tools.
The WordPress website should be updated on a daily basis, according to us. If you’re having trouble keeping up with updates or rolling them out, check out our guide on How to Securely Upgrade Your WordPress Platform.
Harden Your WordPress Site
WordPress.org recommends these steps to harden the WordPress website. This implies that restricting traditional entry points makes your site more secure against hackers. Preventing access attempts, implementing 2-factor authentication, disabling the file editor, stopping plugin installation, and changing passwords and encryption keys are just a few of the measures. Some of these processes, however, are technological in nature, and it is easy to run into hurdles when attempting to carry them out. So, if you’ve installed MalCare, you can take hardening actions right from the dashboard with only a few taps.
Monitor Your Themes and Plugins
The majority of hacks, according to statistics, come through insecure themes and plugins. This has happened multiple times as a result of pirated or null copies of themes and plugins. Despite the fact that these versions are free, malware is still pre-installed on websites. This allows criminals to spread their virus over multiple websites and exploit them.
However, all you’re doing is downloading malware and installing it on your website. We never recommend utilising programmes that have been invalidated. Aside from that, theme and plugin designers work constantly to preserve and update their designs. Engineers, on the other hand, do not upgrade their apps on a regular basis, and they frequently abandon them because they are difficult to operate. You, as the website owner/admin, are in charge of keeping track of the themes and plugins.
Make sure you only utilise the themes and plugins from the WordPress source. Keep an eye on them and make sure they’re updated on a regular basis. Finally, only keep the themes and plugins you use. Delete any disabled ones you may have on your site. This would remove unnecessary parts from the web that could make it vulnerable.
Use An SSL Certificate
While you are operating a website, data is passed between your visitor and your site. Information is transferred between browsers and servers. Personal information, such as the visitor’s usernames and passwords, credit card information, or sensitive details, can be found in any of these data. Hackers utilise a variety of tactics to intercept this data while it is in transit.
To eliminate the potential of this happening, you should utilise an SSL certificate. It encrypts data while it is being processed. Even if a hacker manages to intercept the data, they won’t be able to decipher it because it’s encrypted. Once you’ve implemented these measures, you should be assured that you’ve made the hacker’s task extremely difficult. You may rest easy knowing that your WordPress website is secure. You should also take a few more security precautions, such as banning IP addresses, securing wp-config.php pages, and following this complete WordPress security advice.
FAQs – Repair Hacked Website
Ultimate Thoughts – How to Repair Hacked Website
After cleaning up far too many hijacked WordPress websites, we’ve come to appreciate the agony that webmasters and website owners go through when their site is under attack. Hacked websites have various backdoors, which allow hackers to re-enter and infiltrate a site even after it has been cleansed by security professionals. It is becoming increasingly tough to manage.
It’s as simple as installing MalCare to keep these issues from occurring and to properly clean the web. It will do a web search and delete any harmful traces that may have been left behind. You may now sit back and relax, knowing that the platform is in good hands. MalCare will continue to defend your website from hackers by installing a robust protective firewall and scanning it on a daily basis.